Splunk Integration
How to setup a Splunk integration.
Splunk integration overview
A Splunk integration can be configured to stream your Secberus account activity log data to an installation of Splunk Enterprise or Splunk Cloud Platform using the HTTP Event Collector (HEC).
Notes on the Splunk integration
- There can only be one Splunk integration per Secberus account.
- Only users with the Account Owner role will be able to create Splunk integrations.
Setup a Splunk integration
In order to stream data from Secberus to a Splunk installation, you'll need to create a HEC token in Splunk Web.
- In Splunk Web, log in as an administrator.
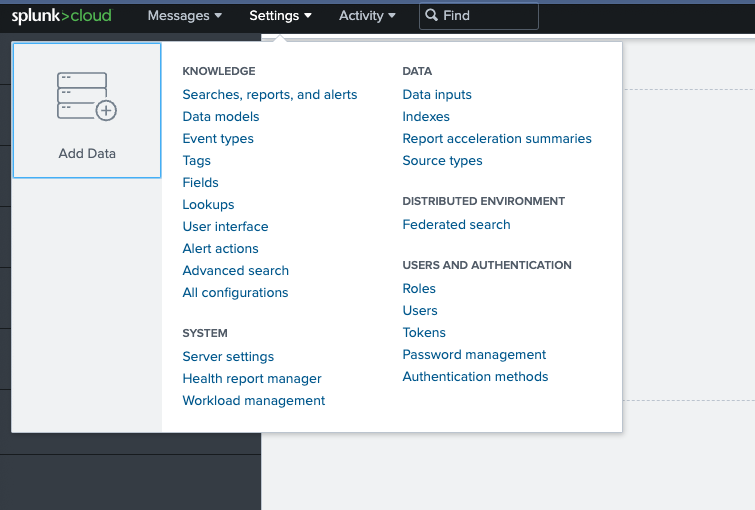
- Go to Settings > Data inputs and select HTTP Event Collector.
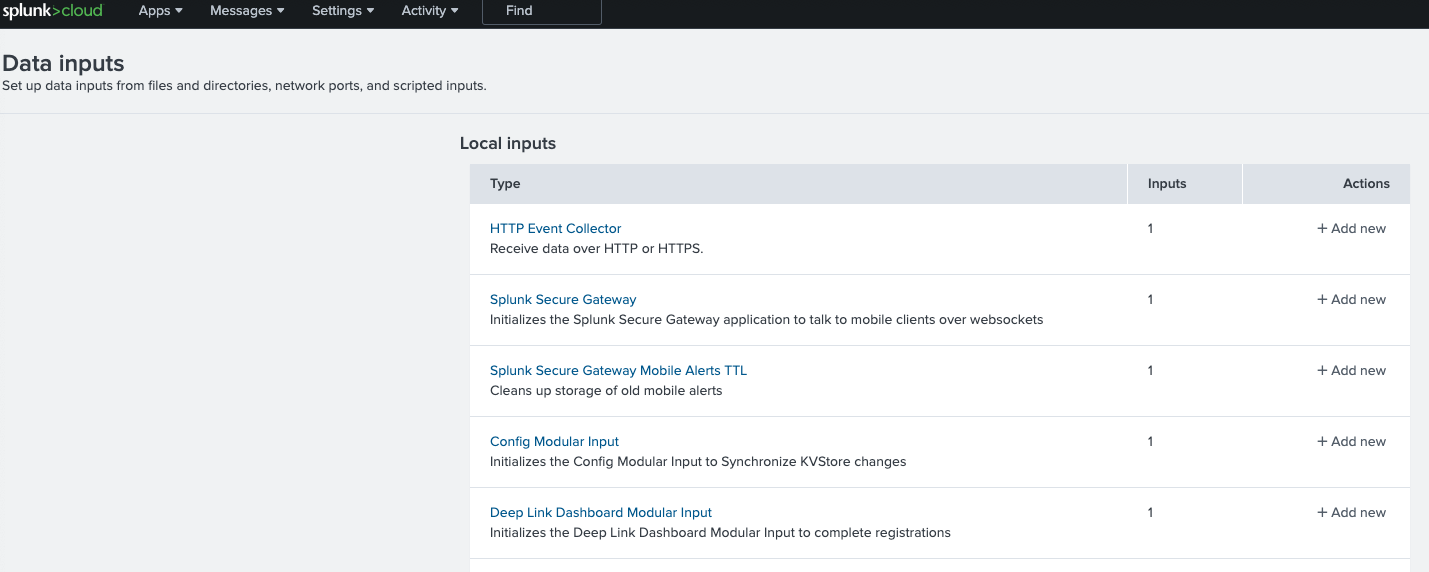
- Click on New Token.
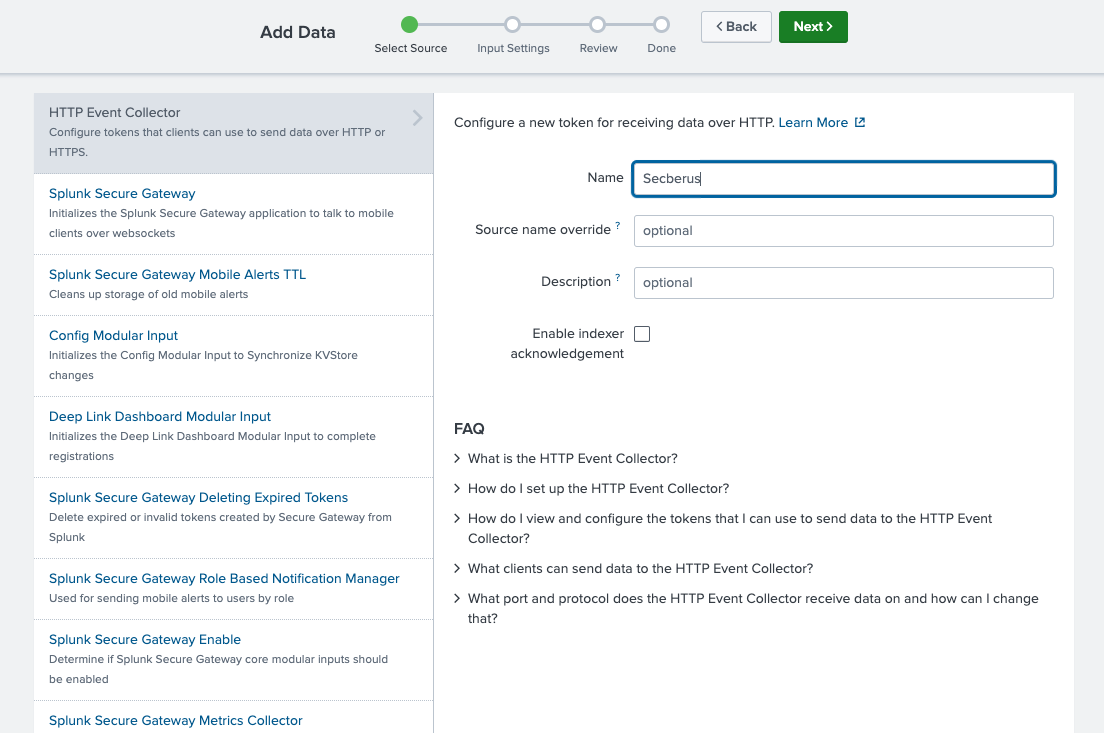
- In the Name field, enter a name for the token.
- (Optional) In the Source name override field, enter a name for a source to be assigned to events that this endpoint generates. Default is 'secberus'.
- (Optional) In the Description field, enter a description for the input.
- (Optional) If you want to enable indexer acknowledgment for this token, click the Enable indexer acknowledgment checkbox.
- Click Next.
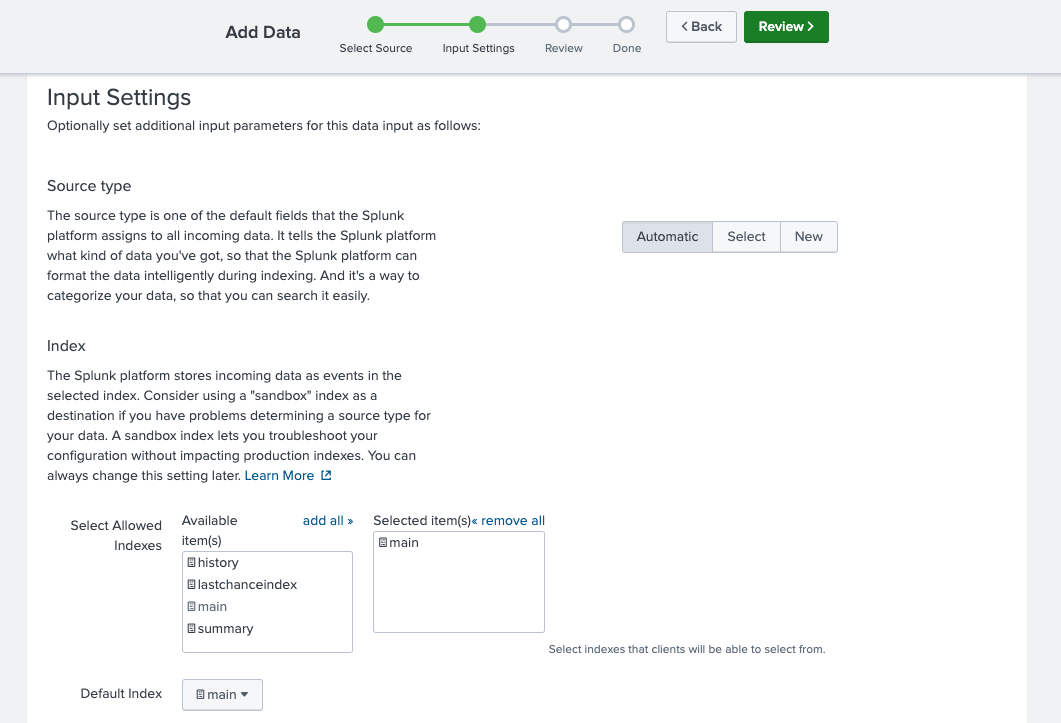
- (Optional) Make edits to source type. Secberus events will have sourcetype '_json' by default.
- Choose the index where you want the Secberus events to be stored. Default is 'main'.
- Click Review.
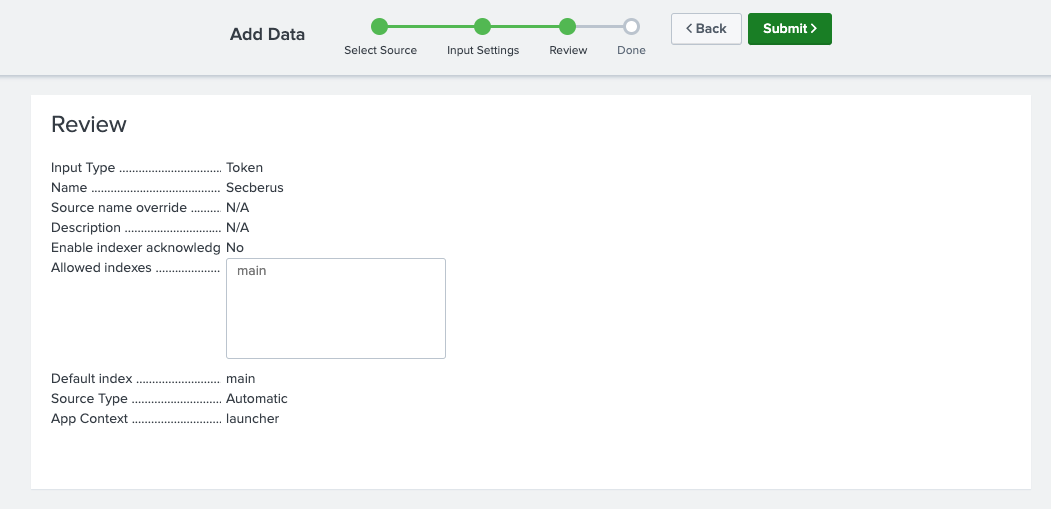
- Confirm that all settings for the endpoint are what you want.
- If all settings are what you want, click Submit. Otherwise, click Back to make changes.
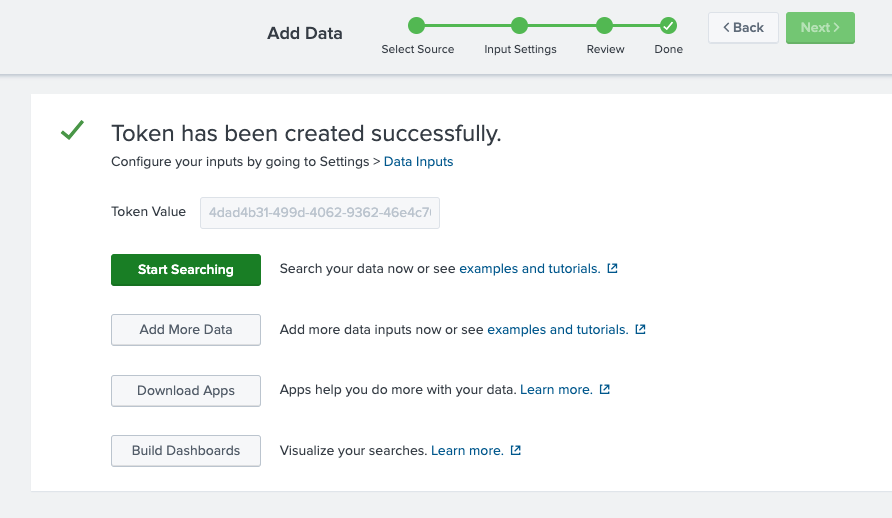
- Copy the token value that Splunk Web displays and the HEC URL from the token settings page.
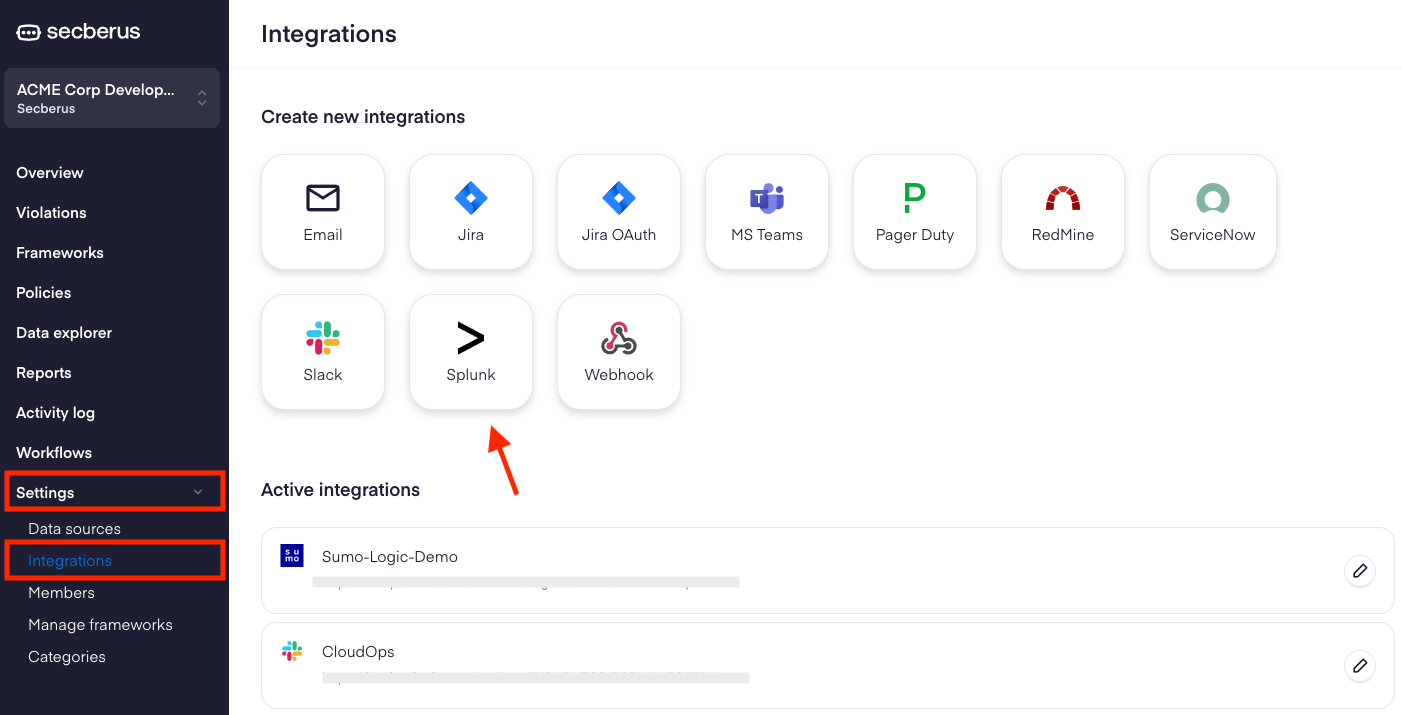
- Within the Secberus application, navigate to Settings > Integrations.
- Click to add a Splunk integration.
- Name the integration and input the HEC URL and Token.
- Include an index to feed the data into. If an index is not entered, the data will feed into the main index by default.
- Click Save.

Splunk integration is now Complete!The Secberus Splunk forwarder will perform a health check on the provided Splunk HEC URL. If the health check comes back successful, Secberus logs will automatically start streaming to the Splunk HEC endpoint within 60 seconds.
Updated 7 months ago